Symptoms
After correctly installing and configuring Authlogics Domain Controller Agent password policy settings are not enforced when a password is changed. Event log entries from Domain Controller Agent are not created and there is no indication that a password change attempt was made.
After enabling Domain Controller Agent Diagnostic Logging the Windows Services and Directory log files are created and populated correctly, however, no DCAgent.log log file is created after a server reboot or a password change attempt.
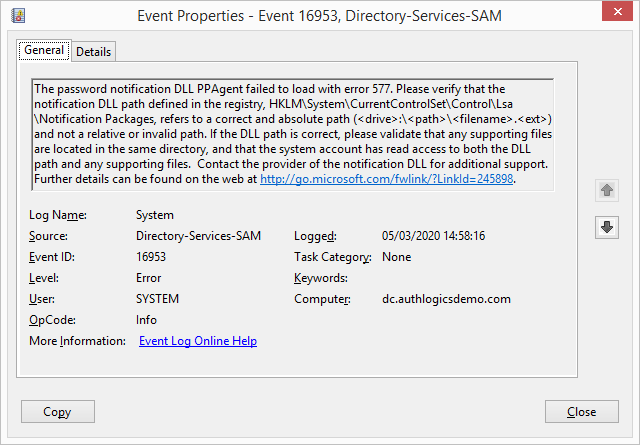
A System Event Log Error entry with ID 16953 from Directory-Services-SAM is logged starting with the text "The password notification DLL DCAgent failed to load with error 577" as follows:
A further System Event Log Information entry with ID 12 from Wininit is logged with the text "LSASS.exe was started as a protected process with level: 4." as follows:

LSASS running a level 4 is evidence of Windows Local Security Authority (LSA) Protection being enabled.
Cause
When Windows Local Security Authority (LSA) Protection is enabled, Windows blocks all 3rd party plugins, including Authlogics Domain Controller Agent, from accessing the Local Security Authority. This Windows feature was designed predominantly for desktop OS's to prevent malware from stealing password hashes, however, the feature is also available on Windows Server.
Further information about LSA protection and its origins can be found here:
- https://docs.microsoft.com/en-us/previous-versions/windows/it-pro/windows-server-2012-R2-and-2012/dn408187(v=ws.11)
- https://www.crowdstrike.com/blog/evolution-protected-processes-part-1-pass-hash-mitigations-windows-81/
How to disable Windows LSA Protection
Enabling LSA Protection is as simple as creating a registry key called RunAsPPL, setting it to 1 and rebooting the server. Furthermore, if the server has a UEFI BIOS the LSA Protection status is also written to a variable in the UEFI configuration. This is done so that malware can not simply disable LSA Protection by removing the RunAsPPL registry key to allow its malicious code to run. However, this extra protection also complicates the LSA Protection removal process for administrators.
Part 1 - Checking the UEFI BIOS status of the server
The first step is to check to see if the servers BIOS mode is set to UEFI.
- Run "msinfo32.exe" to start Microsoft System Information
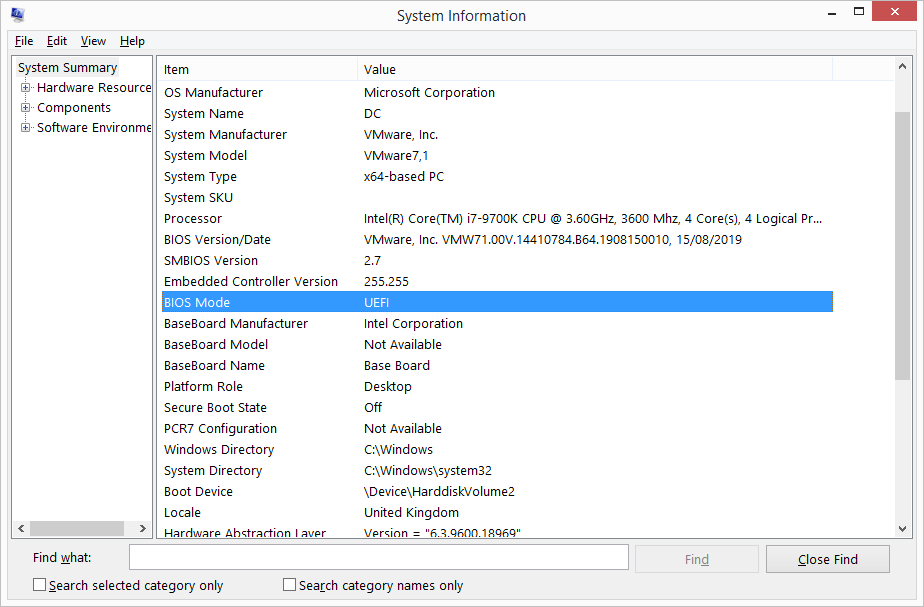
- Check the "BIOS Mode" value.
- If the "BIOS Mode" is NOT "UEFI" then only part 2 of this article is required to be completed, part 3 can be skipped.
- If the "BIOS Mode" is "UEFI" then both part 2 and 3 must be completed to disable LSA Protection.
Part 2 - Removing the RunAsPPL registry key
- Open the Registry Editor (RegEdit.exe), and navigate to the registry key that is located at: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa
- Locate the REG_DWORD value with the name "RunAsPPL" with the data "1".
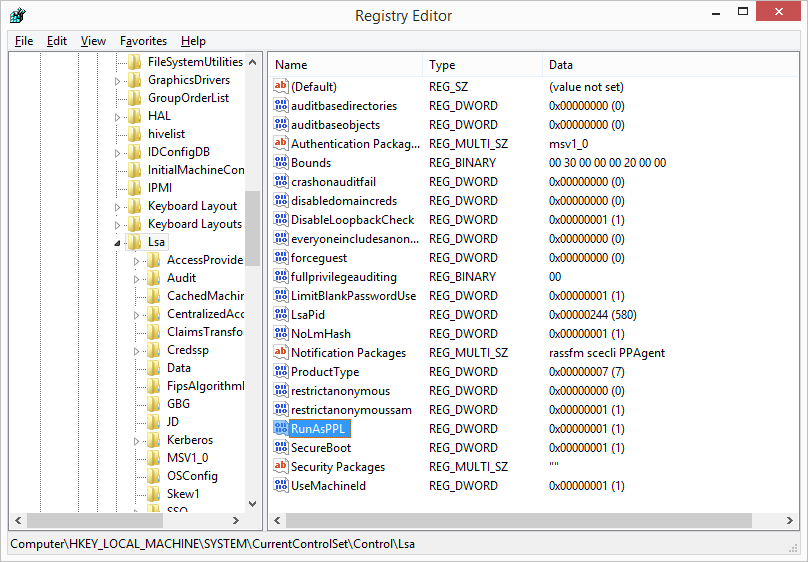
- Delete the registry value entirely.
- Restart the computer.
Part 3 - Update the UEFI configuration
Microsoft has a tool which is designed to reset the LSA Protected variable in a UEFI BIOS . The tool is called the "Local Security Authority (LSA) Protected Process Opt-out tool" and can be downloaded directly from Microsoft.
Note: To perform these steps server console access is required - this can not be done via RDP.
The "install instructions" for the tool on the Microsoft web page are not easy to follow due to a lack of formatting and detail. They have been reproduced and expanded here for clarity:
- Download the LSAPPLConfig files from the download center and save the UEFI tool that corresponds to the architecture of the server to the C:\ drive root.
- Open a Command Prompt as an Administrator and run the following commands to bootstrap the tool:
mountvol X: /s
copy C:\LSAPPLConfig.efi X:\EFI\Microsoft\Boot\LSAPPLConfig.efi /Y
bcdedit /create {0cb3b571-2f2e-4343-a879-d86a476d7215} /d "DebugTool" /application osloader
bcdedit /set {0cb3b571-2f2e-4343-a879-d86a476d7215} path "\EFI\Microsoft\Boot\LSAPPLConfig.efi"
bcdedit /set {bootmgr} bootsequence {0cb3b571-2f2e-4343-a879-d86a476d7215}
bcdedit /set {0cb3b571-2f2e-4343-a879-d86a476d7215} loadoptions %1
bcdedit /set {0cb3b571-2f2e-4343-a879-d86a476d7215} device partition=X:
mountvol X: /d -
Reboot the server and the "LSA Protected Process Opt-out Tool" will start after the reboot.
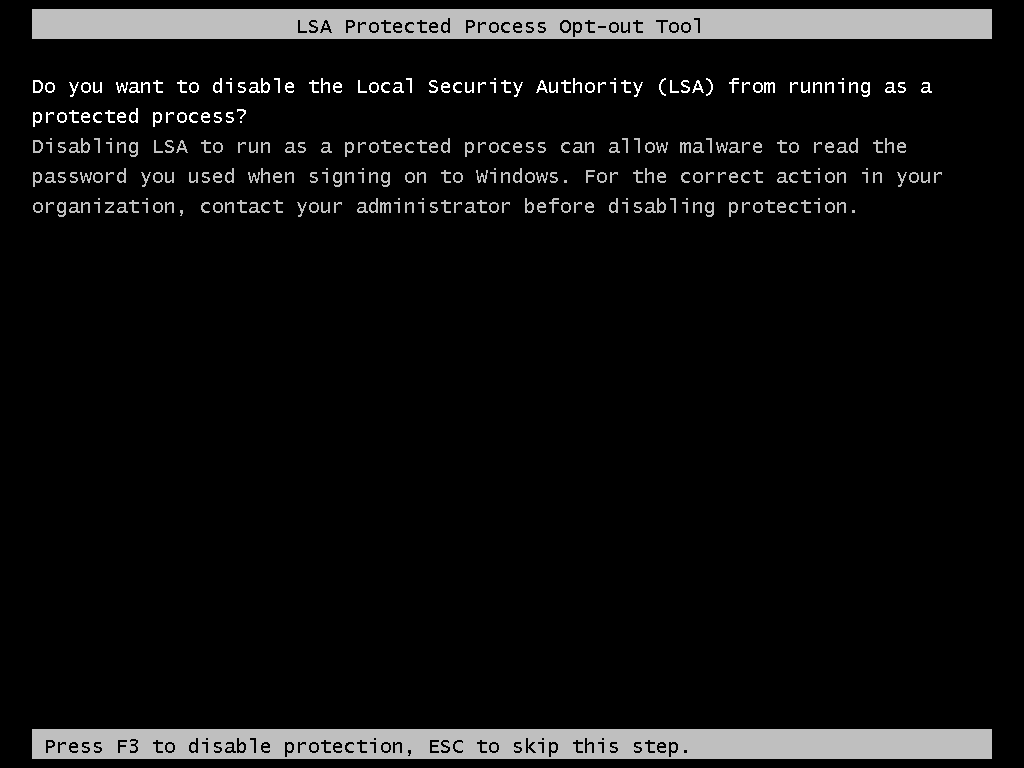
-
Press F3 to accept the change to disable LSA Protection.
Note: If you do not press any key after a short period of time the tool is skipped and you will have to restart the process at step 2.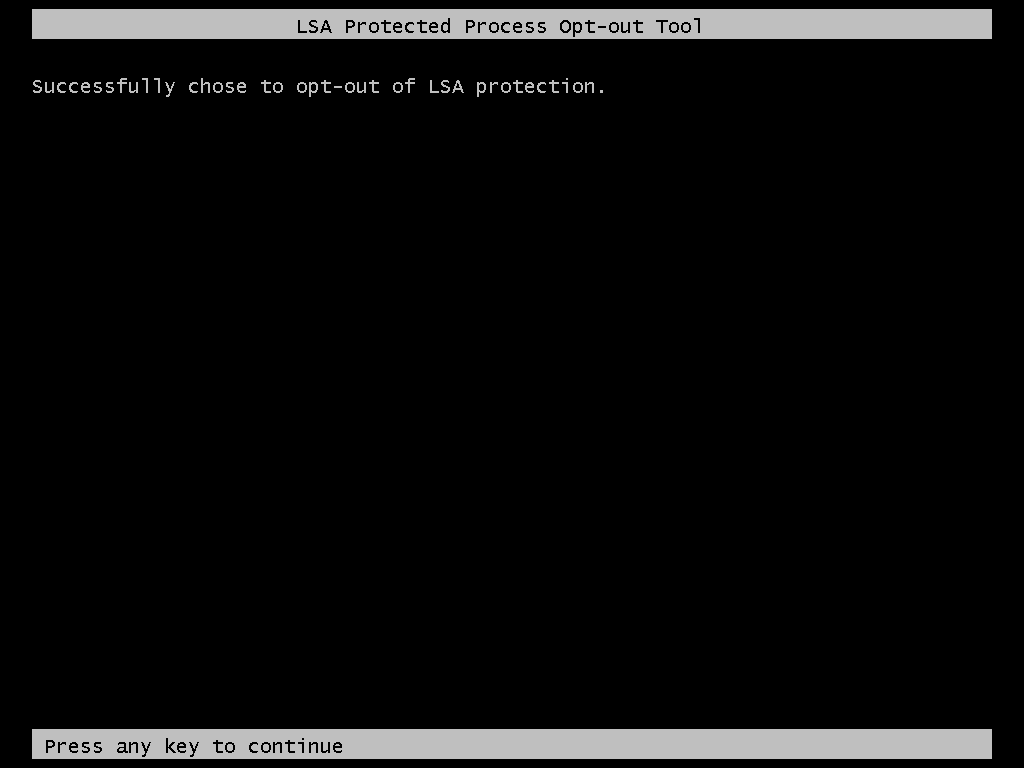
- Press any key to continue. Windows will continue to launch and LSA protection will be disabled.
Part 4 - Ensure LSA Protection is disabled
To ensure that LSA Protection is disabled check that System Event Log Information entry with ID 12 from Wininit is NOT logged after the server reboot.
If Domain Controller Agent Diagnostics Logging is enabled then a PPAgent.log file will be created in the C:\Program Files\Authlogics Domain Controller Agent\Log folder after the reboot.
0 Comments